In 2018, the European Union became the first major international body to institute regulations on internet data protection. The commission’s policy is called the General Data Protection Regulation, or GDPR, and it went into effect as of May 2018.
The rules of GDPR are applicable to any website or online application that can be served to citizens of the EU. So even if your primary audience and data center are located in Australia or the United States, your site can still be held to the regulations.
Whether you are a business owner running an entire company or a junior programmer working on HTML code, you need to take the GDPR rules seriously and integrate them into how your website is run. Ignoring them can result in damaging penalties from the European Commission. Read on for more information on GDPR and the steps to take to stay compliant with data practices.
Basics of GDPR

The concepts behind GDPR were in the works among EU countries for a number of years before the formal release of the regulations. Their primary purpose is to protect the personal information of individuals online and to hold companies accountable for how they manage such data.
The types of data covered by GDPR include email addresses, passwords, phone numbers, mailing addresses, social security numbers, and more. Companies must be transparent with their customers and users about how such information is being stored and tracked, as well as notifying them if any of the data is ever compromised.
Another big facet of GDPR is the idea of data deletion and the right to be forgotten. For many years, online companies argued that once a piece of personal information was posted to the public internet, they could retain it as their permanent property. Under GDPR rules this is no longer the case. Individual people now have the right to request for personal information to be deleted from websites and companies must comply in a timely manner.
If a company is found in violation of GDPR, they are subject to fines of either 10 million euros or four percent of the company’s annual revenue.
Organizational Approach
For small websites such as blogs or hobby pages, staying compliant with GDPR can be as simple as updating your privacy policy and notifying all external users of your compliance with the new regulations. However, larger companies must take additional steps in order to meet EU requirements.
Any organization with more than 15 employees that handles personal information on their local or hosted servers must hire a dedicated data protection officer (DPO). This individual is responsible for overseeing all data storage policies and ensuring they meet the standards of GDPR.
Part of the responsibility for a DPO is to run regular data protection impact assessments (DPIAs). During one of these assessments, the DPO must examine all of the company’s data procedures and identify any risks or concerns.
Handling User Data
For those in a technical role, the first step in gaining GDPR compliance is to make all website visitors aware of your data retention policies. This group of external users includes anyone who navigates to your company’s websites, not just those with a registered account.
Upon their first visit to the website, you must notify them of how their personal data is stored and used on your servers. This notification must also include an actionable consent option, where the individual can choose whether or not they want their personal information to be captured during their session.
As part of GDPR compliance, companies must also offer the ability for users to withdraw their consent at any time. This differs from the right to be forgotten rule, as it blocks companies from storing new information on the individual user but does not require deletion of old data. The exact terms of consent must be documented in a privacy policy, which should be easily found from a website’s homepage and updated on a regular basis.

Individuals who are concerned with how their data is tracked online should think about going to further lengths to protect their identity. Many free open source privacy tools are available, like the TOR browser, which allow you to stay anonymous on the internet. These tools work well with more traditional virtual private network (VPN clients). A VPN service creates a secure channel between a person’s computer and the open internet, with all transmissions fully encrypted. This reduces the risk of a hacker infiltrating your local network and being able to spy on your online activity.
Hosting and Programming
Data storage is a complicated subject due to the popularity of cloud computing. With so much of the public internet being run on virtualized servers through platforms like Amazon Web Services and Microsoft Azure, personal data can end up being located in shared environments.
In order to maximize website security, companies should consider a dedicated server hosting configuration. This means that specific hardware is owned by one company within a data center, while a virtualized private server (VPS) can be merged with other companies’ data and create security risks.
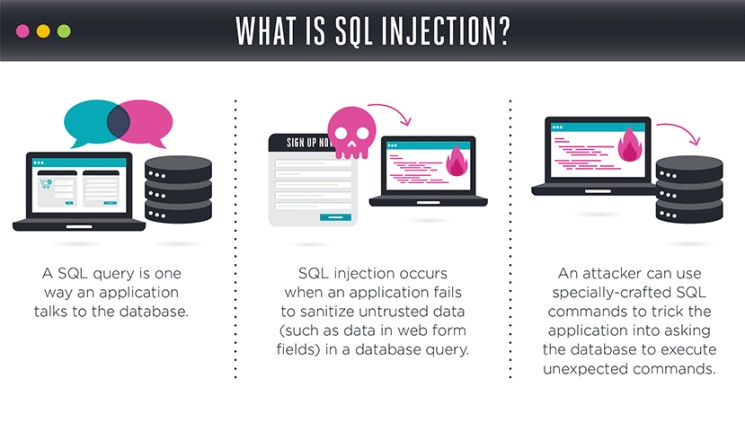
At the code level, developers and programmers need to protect their websites and applications from common vulnerabilities like SQL injections, where a hacker manages to infiltrate an online database by manipulating a URL or input field. If an attacker manages to gain access to records within a database, all user data becomes compromised and a breach notification must be issued as dictated by GDPR rules.
Breach notifications are required for all data loss events, including those resulted from human error or cyber attacks. These alerts must be sent out to all affected users within 72 hours of the event being detected. The notification must detail exactly what categories of information were compromised or lost, how many users are affected, and what the potential effects of the breach could cause.
 Article by Gary Stevens – front end developer, full time blockchain geek and a volunteer working for the Ethereum foundation as well as an active Github contributor.
Article by Gary Stevens – front end developer, full time blockchain geek and a volunteer working for the Ethereum foundation as well as an active Github contributor.